DLP Security and HOPZERO
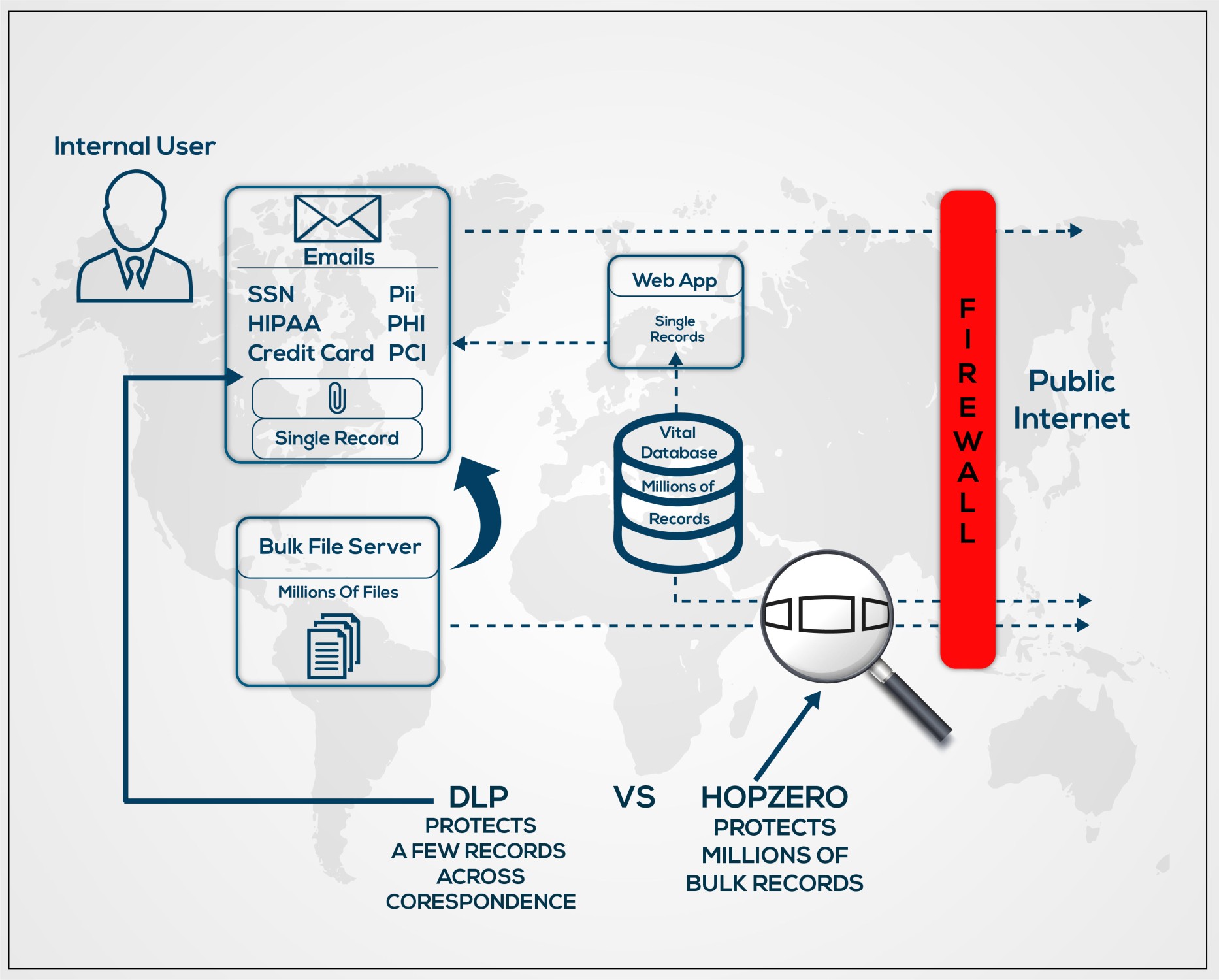
DLP Data Loss Prevention is depicted top left, where a credit card number format, social security number or medical codes are discovered, for instance, as typed text or as a file attachment to an email.
As a second set of electronic eyes, DLP looks for data in correspondence or a web app submission. On detection DLP holds sensitive data, alerting a user and security that sensitive data is leaking individual records.
Today’s applications use multitier environment. It might be two or more tiers deep, Web-tier to Middleware-tier to Database-tier would be called a three-tier architecture. Typically, the first tier is a user computer connecting to a front-end or web-tier system. The web-tier provides user authentication allowing access to only one users data records. The web-tier secondarily connects to the back-end database – but only for one user’s account. The back-end database holds millions of other account-holder’s records not accessible to the logged in user. Multitier architecture protects the full database behind the front-end web-tier.
In contrast HOPZERO identifies and protects an entire back-end “Crown-Jewel” server database similar to DLP, but for the whole server, preventing data exfiltration by containing DataTravel to a small “Sphere of Trust” perimeter, keeping vital data inside the organization.
HOPZERO holds the US patent for managing “packet-lifetime value” inside every data packet header sent from any computer using TCP/IP. The technical term is “time-to-live” TTL or more current, HOP value. HOP value controls and limits how many routers data may traverse. The HOP starts with a large value by default allowing worldwide DataTravel. Each router decrements the HOP value. Most times the packet can go all the way to its intended destination before decrementing to zero, unless it gets lost in the network, in which case HOP decrements to ZERO causing routers to expunge the packet from further travel. Because the default value of every computer is large, all data by default can go worldwide. HOPZERO learns how far data needs to travel to keep it safe inside the datacenter, safe, out of reach of external criminals.
Firewalls provide a packet block at the firewall itself, but only at the firewall. HOPZERO sets the crown-jewel server DataTravel distance that is enforced by any router. Essentially HOPZERO adds a “blocking firewall” at any router in a network path. By setting the limit at the vital server end point, at say 3 routers out, HOPZERO’s system will stop DataTravel at any router three hops away, regardless of a firewalls presence. With HOPZERO, routers act as a block discarding the packets when HOP decrements to ZERO, creating the name: HOPZERO.
HOPZERO learns a smaller distance that lets the data go where needed inside a network – but stops it from going outside. When the HOP value is “0” zero, the packet stops, limiting how far it can travel. That setting keeps vital crown-jewel data inside even when criminals try to take it out – even when firewalls are not there or not properly set.
Small organizations have a few “Crown-Jewel” servers while large organizations have hundreds or thousands of servers that never need to communicate BULK data directly to a user. Users communicate through an intermediary middleware or webapp server. Bulk “backend” databases have millions of sensitive records belonging to millions of other accountholders.
When logging into your bank, the front-end server provides access to only one user’s records through the front-end server. An end user never directly connects to these master databases with millions of sensitive records. Users gain access through the front-end server which brokers user credentials allowing access to only records in the back-end belonging to a single authenticated user.
HOPZERO protects the full back-end bulk bank-account database from a hacker directly connecting and getting the entire database. This is the absolute worst type of data compromise as all data can be exfiltrated through direct connect access to the back-end database. Although criminals might like a few single records, what they most desire are full bulk database access to millions of records.
Critical to daily security operations, DLP watches all user correspondence for single record leaks as depicted in the top left of the diagram. HOPZERO protects all records in the back-end databases criminals are most after as they offer the greatest ransom value.
With HOPZERO, a criminal cannot take a server’s data outside the datacenter or company because the packets stop after traveling the suggested distance HOPZERO sets to protect the data.
Combining both DLP and HOPZERO DataTravel limits completes the most powerful data protection solution. Firewalls provide primary limits, while DLP and HOPZERO provide a secondary method of keeping all data safe inside an organization.
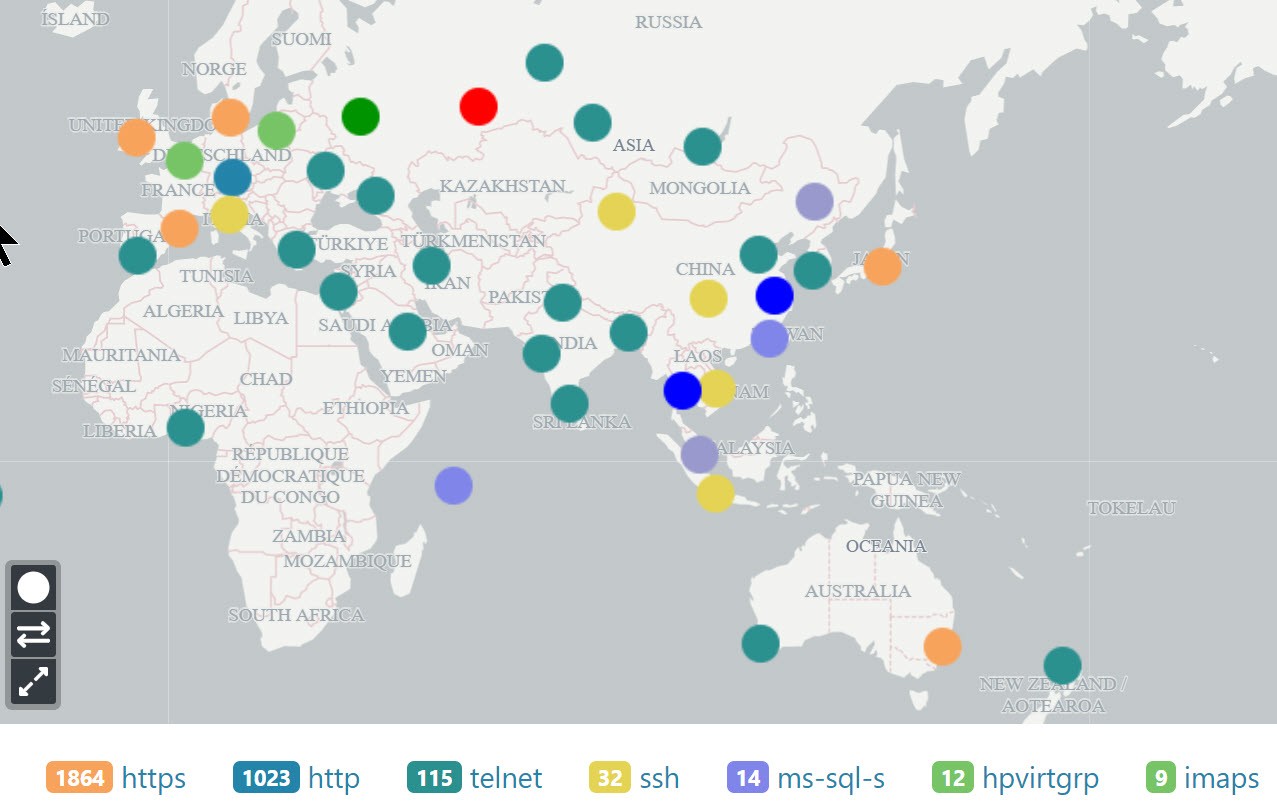
HOPZERO’s visibility maps show where vital data is traveling from every computer inside your internal network or to the Internet worldwide. Seeing where your data is traveling opens eyes to the risk and how to mitigate the risk with DLP and or HOPZERO.
Start your HOPZERO DataTravel adventure mapping where your data is traveling in a few hours.